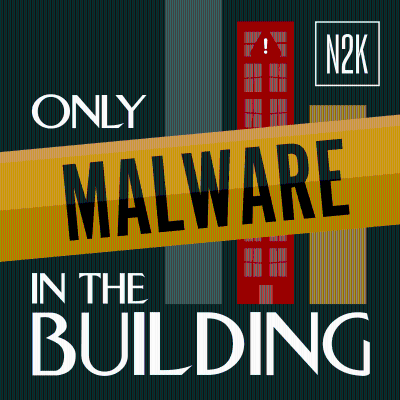
Only Malware in the Building
Podcast by DISCARDED | N2K Networks
"Only Malware in the Building” is a monthly podcast crafted through a collaboration between N2K CyberWire and the Proofpoint DISCARDED podcast. Join y...
Start 7 days free trial
After trial, only 79,00 kr. / month.Cancel anytime.
All episodes
8 episodesWelcome in! You’ve entered, Only Malware in the Building. Grab your eggnog and don your coziest holiday sweater as we sleuth our way through cyber mysteries with a festive twist! Your host is Selena Larson [https://www.linkedin.com/in/selenalarson/], Proofpoint [https://www.proofpoint.com/] intelligence analyst and host of their podcast DISCARDED [https://www.proofpoint.com/us/podcasts/discarded]. Inspired by the residents of a building in New York’s exclusive upper west side, Selena is joined by N2K [https://www.n2k.com/] Networks Dave Bittner [https://www.linkedin.com/in/dave-bittner-27231a4/] and Rick Howard [https://www.linkedin.com/in/rickhoward/] to uncover the stories behind notable cyberattacks. Being a security researcher is a bit like being a detective: you gather clues, analyze the evidence, and consult the experts to solve the cyber puzzle. On this episode, our cyber ghosts delve into the past, present, and future of some of the season’s most pressing threats: two-factor authentication (2FA), social engineering scams, and the return to consumer-targeted attacks. Together, Rick, Dave, and Selena deliver a ghostly—but insightful—message about the state of cybersecurity, past, present, and future. Can their advice save your holiday season from digital disaster? Tune in and find out. May your holidays be merry, bright, and free of cyber fright!
Welcome in! You’ve entered, Only Malware in the Building. Join us each month to sip tea and solve mysteries about today’s most interesting threats. Your host is Selena Larson [https://www.linkedin.com/in/selenalarson/], Proofpoint [https://www.proofpoint.com/] intelligence analyst and host of their podcast DISCARDED [https://www.proofpoint.com/us/podcasts/discarded]. Inspired by the residents of a building in New York’s exclusive upper west side, Selena is joined by N2K [https://www.n2k.com/] Networks Dave Bittner [https://www.linkedin.com/in/dave-bittner-27231a4/] and Rick Howard [https://www.linkedin.com/in/rickhoward/] to uncover the stories behind notable cyberattacks. Being a security researcher is a bit like being a detective: you gather clues, analyze the evidence, and consult the experts to solve the cyber puzzle. On this episode, we talk about how threat actors are shifting tactics across the landscape, focusing more on advanced social engineering and refined initial access strategies than on sophisticated malware. We’ll dive into Proofpoint's latest blog [https://www.proofpoint.com/us/blog/threat-insight/security-brief-actor-uses-compromised-accounts-customized-social-engineering] detailing a transport sector breach that, while involving relatively standard malware, showcases this growing trend of nuanced techniques and toolsets.
Welcome, witches, wizards, and cybersecurity sleuths! You’ve entered, Only Malware in the Building. Join us each month to brew potions of knowledge and crack the curses of today’s most intriguing cyber mysteries. Your host is Selena Larson [https://www.linkedin.com/in/selenalarson/], Proofpoint [https://www.proofpoint.com/] intelligence analyst and host of their podcast DISCARDED [https://www.proofpoint.com/us/podcasts/discarded]. Inspired by the residents of a building in New York’s exclusive upper west side, Selena is joined by N2K [https://www.n2k.com/] Networks Dave Bittner [https://www.linkedin.com/in/dave-bittner-27231a4/] and Rick Howard [https://www.linkedin.com/in/rickhoward/] to uncover the stories behind notable cyberattacks. Being a security researcher is a bit like being a detective: you gather clues, analyze the evidence, and consult the experts to solve the cyber puzzle. On this episode, we dive into how Proofpoint [https://www.proofpoint.com/us] researchers uncovered an espionage campaign casting custom malware known as "Voldemort [https://www.proofpoint.com/us/blog/threat-insight/malware-must-not-be-named-suspected-espionage-campaign-delivers-voldemort]" in August 2024. The Dark Arts practitioner behind this campaign targeted global organizations, disguising themselves as mundane tax authorities and weaving clever enchantments like using Google Sheets for command and control (C2). While their ultimate motive remains as shadowy as a cursed Horcrux, this malware is built for intelligence gathering and is primed to unleash additional attacks — likely summoning something even darker, like Cobalt Strike. Prepare your wands, and let’s dive into this tale of digital sorcery!
Welcome in! You’ve entered, Only Malware in the Building. Join us each month to sip tea and solve mysteries about today’s most interesting threats. Your host is Selena Larson [https://www.linkedin.com/in/selenalarson/], Proofpoint [https://www.proofpoint.com/] intelligence analyst and host of their podcast DISCARDED [https://www.proofpoint.com/us/podcasts/discarded]. Inspired by the residents of a building in New York’s exclusive upper west side, Selena is joined by N2K [https://www.n2k.com/] Networks Dave Bittner [https://www.linkedin.com/in/dave-bittner-27231a4/] and Rick Howard [https://www.linkedin.com/in/rickhoward/] to uncover the stories behind notable cyberattacks. Being a security researcher is a bit like being a detective: you gather clues, analyze the evidence, and consult the experts to solve the cyber puzzle. On this episode, we talk about the abuse of legitimate services for malware delivery. Proofpoint has seen an increase in the abuse of tools like ScreenConnect and NetSupport, as well as Cloudflare Tunnel [https://www.proofpoint.com/us/blog/threat-insight/threat-actor-abuses-cloudflare-tunnels-deliver-rats] abuse and the use of IP filtering. They have also observed a rise in financially motivated malware delivery using TryCloudflare Tunnel abuse, focusing on remote access trojans (RATs) like Xworm and AsyncRAT. Today we look at how Cloudflare tunnels are used to evade detection and how they have evolved their tactics by incorporating obfuscation techniques, with ongoing research to identify the threat actors involved.
Welcome in! You’ve entered, Only Malware in the Building. Join us each month to sip tea and solve mysteries about today’s most interesting threats. Your host is Selena Larson [https://www.linkedin.com/in/selenalarson/], Proofpoint [https://www.proofpoint.com/] intelligence analyst and host of their podcast DISCARDED [https://www.proofpoint.com/us/podcasts/discarded]. Inspired by the residents of a building in New York’s exclusive upper west side, Selena is joined by N2K [https://www.n2k.com/] Networks Dave Bittner [https://www.linkedin.com/in/dave-bittner-27231a4/] and Rick Howard [https://www.linkedin.com/in/rickhoward/] to uncover the stories behind notable cyberattacks. Being a security researcher is a bit like being a detective: you gather clues, analyze the evidence, and consult the experts to solve the cyber puzzle. On this episode, we talk about the use of AI in cyberattacks Proofpoint recently released two articles on two cyber campaigns: one by the group UNK_SweetSpecter targeting U.S. organizations involved in AI with the SugarGh0st RAT [https://www.proofpoint.com/us/blog/threat-insight/security-brief-artificial-sweetener-sugargh0st-rat-used-target-american], and another by TA547 [https://www.proofpoint.com/us/blog/threat-insight/security-brief-ta547-targets-german-organizations-rhadamanthys-stealer] targeting German organizations with Rhadamanthys malware. Today we look at what the focus of threat actor objectives are and what that means for defenders.
Available everywhere
Listen to Podimo on your phone, tablet, computer or car!
A universe of audio entertainment
Thousands of audiobooks and exclusive podcasts
No ads
Don't waste time listening to ad breaks when listening to Podimo's content.
Start 7 days free trial
After trial, only 79,00 kr. / month.Cancel anytime.
Exclusive podcasts
Ad free
Non-Podimo podcasts
Audiobooks
20 hours / month